Citizen Lab researchers say they have found evidence that dozens of journalists had their iPhones silently compromised with spyware known to be used by nation states.
For more than the past year, London-based reporter Rania Dridi and at least 36 journalists, producers and executives working for the Al Jazeera news agency were targeted with a so-called “zero-click” attack that exploited a now-fixed vulnerability in Apple’s iMessage. The attack invisibly compromised the devices without having to trick the victims into opening a malicious link.
Citizen Lab, the internet watchdog at the University of Toronto, was asked to investigate earlier this year after one of the victims, Al Jazeera investigative journalist Tamer Almisshal, suspected that his phone may have been hacked.
In a technical report out Sunday and shared with TechCrunch, the researchers say they believe the journalists’ iPhones were infected with the Pegasus spyware, developed by Israel-based NSO Group.
The researchers analyzed Almisshal’s iPhone and found it had between July and August connected to servers known to be used by NSO for delivering the Pegasus spyware. The device revealed a burst of network activity that suggests that the spyware may have been delivered silently over iMessage.
Logs from the phone show that the spyware was likely able to secretly record the microphone and phone calls, take photos using the phone’s camera, access the victim’s passwords, and track the phone’s location.
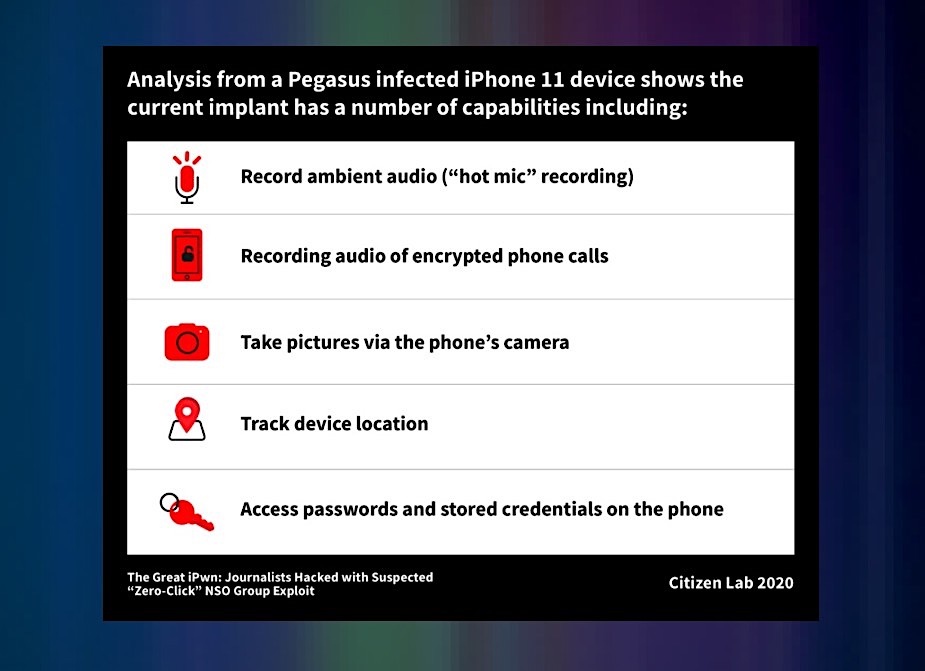
Citizen Lab analyzed the network logs of two hacked iPhones and found it could record ambient calls, take photos using the camera, and track the device’s location without the victim knowing. (Image: Citizen Lab)
Citizen Lab said the bulk of the hacks were likely carried out by at least four NSO customers, including the governments of Saudi Arabia and the United Arab Emirates, citing evidence it found in similar attacks involving Pegasus.
The researchers found evidence that two other NSO customers hacked into one and three Al Jazeera phones respectively, but that they could not attribute the attacks to a specific government.
A spokesperson for Al Jazeera, which just broadcast its reporting of the hacks, did not immediately comment.
NSO sells governments and nation states access to its Pegasus spyware as a prepackaged service by providing the infrastructure and the exploits needed to launch the spyware against the customer’s targets. But the spyware maker has repeatedly distanced itself from what its customers do and has said it does not who its customers target. Some of NSO’s known customers include authoritarian regimes like China and Russia. Saudi Arabia allegedly used the surveillance technology to spy on the communications of columnist Jamal Khashoggi shortly before his murder, which U.S. intelligence concluded was likely ordered by the kingdom’s de facto ruler, Crown Prince Mohammed bin Salman.
Citizen Lab said it also found evidence that Dridi, a journalist at Arabic television station Al Araby in London, had fallen victim to a zero-click attack. The researchers said Dridi was likely targeted by the UAE government.
In a phone call, Dridi told TechCrunch that her phone may have been targeted because of her close association to a person of interest to the UAE.
Dridi’s phone, an iPhone XS Max, was targeted for a longer period, likely between October 2019 and July 2020. The researchers found evidence that she was targeted on two separate occasions with a zero-day attack — the name of an exploit that has not been previously disclosed and that a patch is not yet available — because her phone was running the latest version of iOS both times.
“My life is not normal anymore. I don’t feel like I have a private life again,” said Dridi. “To be a journalist is not a crime,” she said.
Citizen Lab said its latest findings reveal an “accelerating trend of espionage” against journalists and news organizations, and that the growing use of zero-click exploits makes it increasingly difficult — though evidently not impossible — to detect because of the more sophisticated techniques used to infect victims’ devices while covering their tracks.
When reached on Saturday, NSO said it was unable to comment on the allegations as it had not seen the report, but declined to say when asked if Saudi Arabia or the UAE were customers or describe what processes — if any — it puts in place to prevent customers from targeting journalists.
“This is the first we are hearing of these assertions. As we have repeatedly stated, we do not have access to any information related to the identities of individuals upon whom our system is alleged to have been used to conduct surveillance. However, when we receive credible evidence of misuse, combined with the basic identifiers of the alleged targets and timeframes, we take all necessary steps in accordance with our product misuse investigation procedure to review the allegations,” said a spokesperson.
“We are unable to comment on a report we have not yet seen. We do know that CitizenLab regularly publishes reports based on inaccurate assumptions and without a full command of the facts, and this report will likely follow that theme NSO provides products that enable governmental law enforcement agencies to tackle serious organized crime and counterterrorism only, but as stated in the past, we do not operate them. Nevertheless, we are committed to ensuring our policies are adhered to, and any evidence of a breach will be taken seriously and investigated.”
Citizen Lab said it stood by its findings.
Spokespeople for the Saudi and UAE governments in New York did not respond to an email requesting comment.
The attacks not only puts a renewed focus on the shadowy world of surveillance spyware, but also the companies having to defend against it. Apple rests much of its public image on advocating privacy for its users and building secure devices, like iPhones, designed to be hardened against the bulk of attacks. But no technology is impervious to security bugs. In 2016, Reuters reported that UAE-based cybersecurity firm DarkMatter bought a zero-click exploit to target iMessage, which they referred to as “Karma.” The exploit worked even if the user did not actively use the messaging app.
Apple told TechCrunch that it had not independently verified Citizen Lab’s findings but that the vulnerabilities used to target the reporters were fixed in iOS 14, released in September.
“At Apple, our teams work tirelessly to strengthen the security of our users’ data and devices. iOS 14 is a major leap forward in security and delivered new protections against these kinds of attacks. The attack described in the research was highly targeted by nation-states against specific individuals. We always urge customers to download the latest version of the software to protect themselves and their data,” said an Apple spokesperson.
NSO is currently embroiled in a legal battle with Facebook, which last year blamed the Israeli spyware maker for using a similar, previously undisclosed zero-click exploit in WhatsApp to infect some 1,400 devices with the Pegasus spyware.
Facebook discovered and patched the vulnerability, stopping the attack in its tracks, but said that more than 100 human rights defenders, journalists and “other members of civil society” had fallen victim.